CISSP Exam Questions - Online Test
CISSP Premium VCE File

150 Lectures, 20 Hours
It is more faster and easier to pass the cissp exam fee by using cissp certification cost. Immediate access to the cissp study guide and find the same core area cissp salary with professionally verified answers, then PASS your exam with a high score now.
Free CISSP Demo Online For Microsoft Certifitcation:
NEW QUESTION 1
When evaluating third-party applications, which of the following is the GREATEST responsibility of Information Security?
- A. Accept the risk on behalf of the organization.
- B. Report findings to the business to determine security gaps.
- C. Quantify the risk to the business for product selection.
- D. Approve the application that best meets security requirements.
Answer: C
NEW QUESTION 2
Which security service is served by the process of encryption plaintext with the sender’s private key and decrypting cipher text with the sender’s public key?
- A. Confidentiality
- B. Integrity
- C. Identification
- D. Availability
Answer: A
NEW QUESTION 3
In which order, from MOST to LEAST impacted, does user awareness training reduce the occurrence of the events below?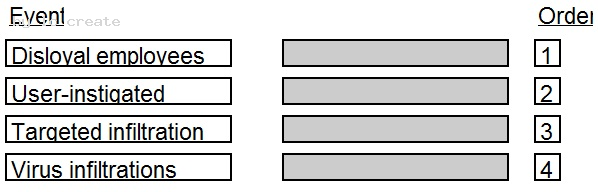
Answer:
Explanation: 
Topic 12, NEW QUESTIONS A
NEW QUESTION 4
Which of the following is the MOST important part of an awareness and training plan to prepare employees for emergency situations?
- A. Having emergency contacts established for the general employee population to get information
- B. Conducting business continuity and disaster recovery training for those who have a direct role in the recovery
- C. Designing business continuity and disaster recovery training programs for different audiences
- D. Publishing a corporate business continuity and disaster recovery plan on the corporate website
Answer: C
NEW QUESTION 5
As one component of a physical security system, an Electronic Access Control (EAC) token is BEST known for its ability to
- A. overcome the problems of key assignments.
- B. monitor the opening of windows and doors.
- C. trigger alarms when intruders are detected.
- D. lock down a facility during an emergency.
Answer: A
NEW QUESTION 6
Which of the following is an essential element of a privileged identity lifecycle management?
- A. Regularly perform account re-validation and approval
- B. Account provisioning based on multi-factor authentication
- C. Frequently review performed activities and request justification
- D. Account information to be provided by supervisor or line manager
Answer: A
NEW QUESTION 7
Which of the following MUST be part of a contract to support electronic discovery of data stored in a cloud environment?
- A. Integration with organizational directory services for authentication
- B. Tokenization of data
- C. Accommodation of hybrid deployment models
- D. Identification of data location
Answer: D
NEW QUESTION 8
Which of the following does Temporal Key Integrity Protocol (TKIP) support?
- A. Multicast and broadcast messages
- B. Coordination of IEEE 802.11 protocols
- C. Wired Equivalent Privacy (WEP) systems
- D. Synchronization of multiple devices
Answer: C
NEW QUESTION 9
An organization recently conducted a review of the security of its network applications. One of the vulnerabilities found was that the session key used in encrypting sensitive information to a third party server
had been hard-coded in the client and server applications. Which of the following would be MOST effective in mitigating this vulnerability?
- A. Diffle-Hellman (DH) algorithm
- B. Elliptic Curve Cryptography (ECC) algorithm
- C. Digital Signature algorithm (DSA)
- D. Rivest-Shamir-Adleman (RSA) algorithm
Answer: A
NEW QUESTION 10
Which of the following could be considered the MOST significant security challenge when adopting DevOps practices compared to a more traditional control framework?
- A. Achieving Service Level Agreements (SLA) on how quickly patches will be released when a security flaw is found.
- B. Maintaining segregation of duties.
- C. Standardized configurations for logging, alerting, and security metrics.
- D. Availability of security teams at the end of design process to perform last-minute manual audits and reviews.
Answer: B
NEW QUESTION 11
A large university needs to enable student access to university resources from their homes. Which of the following provides the BEST option for low maintenance and ease of deployment?
- A. Provide students with Internet Protocol Security (IPSec) Virtual Private Network (VPN) client software.
- B. Use Secure Sockets Layer (SSL) VPN technology.
- C. Use Secure Shell (SSH) with public/private keys.
- D. Require students to purchase home router capable of VPN.
Answer: B
NEW QUESTION 12
Which of the following techniques is known to be effective in spotting resource exhaustion problems, especially with resources such as processes, memory, and connections?
- A. Automated dynamic analysis
- B. Automated static analysis
- C. Manual code review
- D. Fuzzing
Answer: A
NEW QUESTION 13
Drag the following Security Engineering terms on the left to the BEST definition on the right.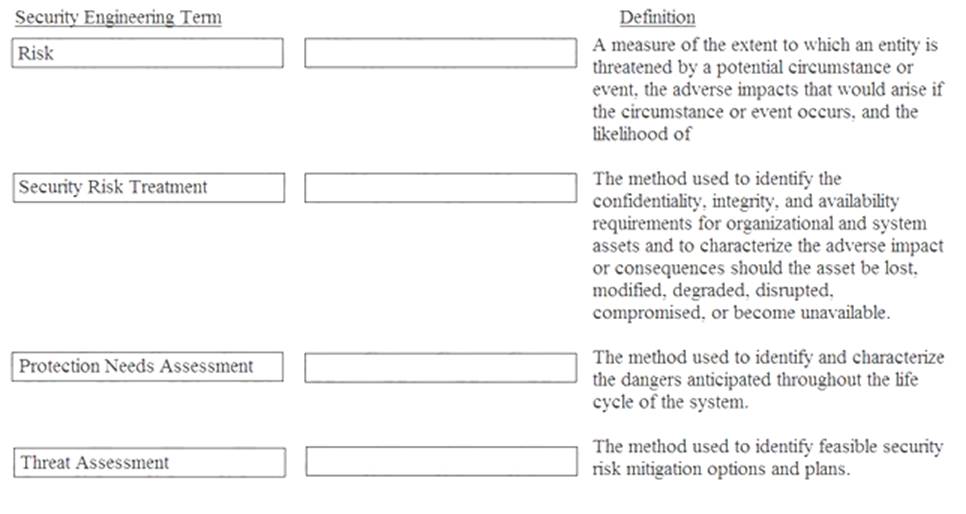
Answer:
Explanation: Risk - A measure of the extent to which an entity is threatened by a potential circumstance of event, the adverse impacts that would arise if the circumstance or event occurs, and the likelihood of occurrence.
Protection Needs Assessment - The method used to identify the confidentiality, integrity, and availability requirements for organizational and system assets and to characterize the adverse impact or consequences should be asset be lost, modified, degraded, disrupted, compromised, or become unavailable.
Threat assessment - The method used to identify and characterize the dangers anticipated throughout the life cycle of the system.
Security Risk Treatment - The method used to identify feasible security risk mitigation options and plans.
NEW QUESTION 14
Refer to the information below to answer the question.
An organization experiencing a negative financial impact is forced to reduce budgets and the number of Information Technology (IT) operations staff performing basic logical access security administration functions. Security processes have been tightly integrated into normal IT operations and are not separate and distinct roles.
Which of the following will indicate where the IT budget is BEST allocated during this time?
- A. Policies
- B. Frameworks
- C. Metrics
- D. Guidelines
Answer: C
NEW QUESTION 15
Refer to the information below to answer the question.
During the investigation of a security incident, it is determined that an unauthorized individual accessed a system which hosts a database containing financial information.
If the intrusion causes the system processes to hang, which of the following has been affected?
- A. System integrity
- B. System availability
- C. System confidentiality
- D. System auditability
Answer: B
NEW QUESTION 16
The PRIMARY outcome of a certification process is that it provides documented
- A. system weaknesses for remediation.
- B. standards for security assessment, testing, and process evaluation.
- C. interconnected systems and their implemented security controls.
- D. security analyses needed to make a risk-based decision.
Answer: D
NEW QUESTION 17
Which of the following is the MOST difficult to enforce when using cloud computing?
- A. Data access
- B. Data backup
- C. Data recovery
- D. Data disposal
Answer: D
P.S. Certleader now are offering 100% pass ensure CISSP dumps! All CISSP exam questions have been updated with correct answers: https://www.certleader.com/CISSP-dumps.html (653 New Questions)
- The Secret Of ISC2 SSCP Preparation Labs
- Refined CCSP Braindumps 2021
- Improved CISSP-ISSMP Training Tools 2021
- ISC2 CISSP Exam Dumps 2021
- Top Tips Of Improved SSCP Free Exam
- ISC2 CCSP Exam Questions and Answers 2021
- High quality CCSP Exam Questions and Answers 2021
- ISC2 CISSP Braindumps 2021
- ISC2 CCSP Exam Dumps 2021
- Vivid ISC2 SSCP Dump Online


