200-201 Exam Questions - Online Test
200-201 Premium VCE File

150 Lectures, 20 Hours
Our pass rate is high to 98.9% and the similarity percentage between our 200-201 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Cisco 200-201 exam in just one try? I am currently studying for the Cisco 200-201 exam. Latest Cisco 200-201 Test exam practice questions and answers, Try Cisco 200-201 Brain Dumps First.
Online 200-201 free questions and answers of New Version:
NEW QUESTION 1
Which NIST IR category stakeholder is responsible for coordinating incident response among various business units, minimizing damage, and reporting to regulatory agencies?
- A. CSIRT
- B. PSIRT
- C. public affairs
- D. management
Answer: D
NEW QUESTION 2
Which data format is the most efficient to build a baseline of traffic seen over an extended period of time?
- A. syslog messages
- B. full packet capture
- C. NetFlow
- D. firewall event logs
Answer: C
NEW QUESTION 3
A security engineer deploys an enterprise-wide host/endpoint technology for all of the company's corporate PCs. Management requests the engineer to block a selected set of applications on all PCs.
Which technology should be used to accomplish this task?
- A. application whitelisting/blacklisting
- B. network NGFW
- C. host-based IDS
- D. antivirus/antispyware software
Answer: A
NEW QUESTION 4
Refer to the exhibit.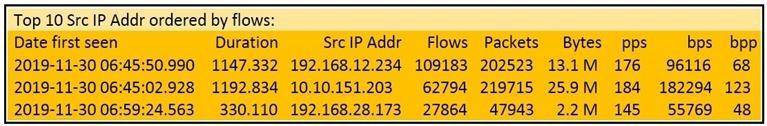
What information is depicted?
- A. IIS data
- B. NetFlow data
- C. network discovery event
- D. IPS event data
Answer: B
NEW QUESTION 5
Which security principle is violated by running all processes as root or administrator?
- A. principle of least privilege
- B. role-based access control
- C. separation of duties
- D. trusted computing base
Answer: A
NEW QUESTION 6
What should a security analyst consider when comparing inline traffic interrogation with traffic tapping to determine which approach to use in the network?
- A. Tapping interrogation replicates signals to a separate port for analyzing traffic
- B. Tapping interrogations detect and block malicious traffic
- C. Inline interrogation enables viewing a copy of traffic to ensure traffic is in compliance with security policies
- D. Inline interrogation detects malicious traffic but does not block the traffic
Answer: A
NEW QUESTION 7
Refer to the exhibit.
Which two elements in the table are parts of the 5-tuple? (Choose two.)
- A. First Packet
- B. Initiator User
- C. Ingress Security Zone
- D. Source Port
- E. Initiator IP
Answer: DE
NEW QUESTION 8
Refer to the exhibit.
Which packet contains a file that is extractable within Wireshark?
- A. 2317
- B. 1986
- C. 2318
- D. 2542
Answer: D
NEW QUESTION 9
Which artifact is used to uniquely identify a detected file?
- A. file timestamp
- B. file extension
- C. file size
- D. file hash
Answer: D
NEW QUESTION 10
Which type of data consists of connection level, application-specific records generated from network traffic?
- A. transaction data
- B. location data
- C. statistical data
- D. alert data
Answer: A
NEW QUESTION 11
What is the difference between deep packet inspection and stateful inspection?
- A. Deep packet inspection is more secure than stateful inspection on Layer 4
- B. Stateful inspection verifies contents at Layer 4 and deep packet inspection verifies connection at Layer 7
- C. Stateful inspection is more secure than deep packet inspection on Layer 7
- D. Deep packet inspection allows visibility on Layer 7 and stateful inspection allows visibility on Layer 4
Answer: D
NEW QUESTION 12
An analyst is investigating a host in the network that appears to be communicating to a command and control server on the Internet. After collecting this packet capture the analyst cannot determine the technique and payload used for the communication.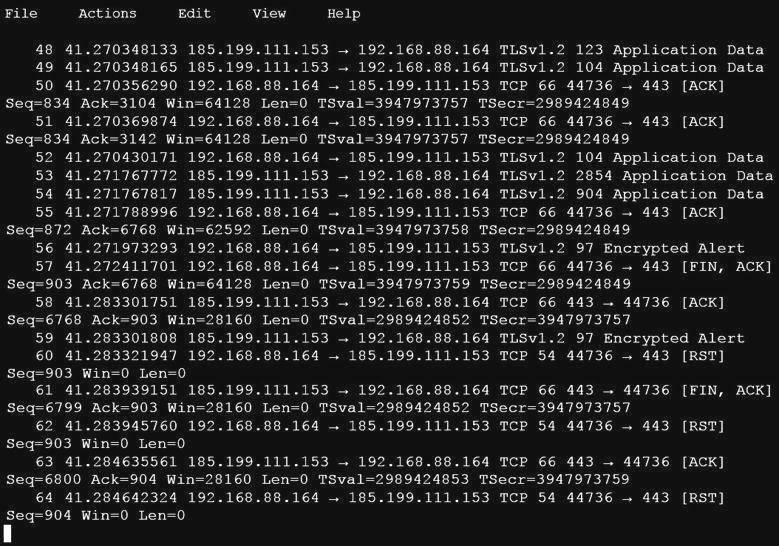
Which obfuscation technique is the attacker using?
- A. Base64 encoding
- B. transport layer security encryption
- C. SHA-256 hashing
- D. ROT13 encryption
Answer: B
NEW QUESTION 13
Which type of attack occurs when an attacker is successful in eavesdropping on a conversation between two IP phones?
- A. known-plaintext
- B. replay
- C. dictionary
- D. man-in-the-middle
Answer: D
NEW QUESTION 14
What is the virtual address space for a Windows process?
- A. physical location of an object in memory
- B. set of pages that reside in the physical memory
- C. system-level memory protection feature built into the operating system
- D. set of virtual memory addresses that can be used
Answer: D
NEW QUESTION 15
Which regex matches only on all lowercase letters?
- A. [az]+
- B. [^az]+
- C. az+
- D. a*z+
Answer: A
NEW QUESTION 16
......
P.S. Easily pass 200-201 Exam with 98 Q&As Dumps-files.com Dumps & pdf Version, Welcome to Download the Newest Dumps-files.com 200-201 Dumps: https://www.dumps-files.com/files/200-201/ (98 New Questions)
- A Review Of Actual 400-051 dumps
- The Up To The Immediate Present Guide To 400-007 Exam Question
- Cisco 200-155 Questions 2021
- What Simulation 400-051 vce Is?
- how many questions of 210-451 dumps?
- A Review Of Approved 300-206 vce
- Top Quality CCNP Collaboration 300-075 dumps
- What Realistic 300-070 dumps Is?
- A Review Of High quality 400-051 examcollection
- Verified CCNP Security 300-208 exam dumps


