PCNSE Exam Questions - Online Test
PCNSE Premium VCE File

150 Lectures, 20 Hours
Master the PCNSE Palo Alto Networks Certified Security Engineer (PCNSE)PAN-OS 8.0 content and be ready for exam day success quickly with this Pass4sure PCNSE rapidshare. We guarantee it!We make it a reality and give you real PCNSE questions in our Paloalto-Networks PCNSE braindumps.Latest 100% VALID Paloalto-Networks PCNSE Exam Questions Dumps at below page. You can use our Paloalto-Networks PCNSE braindumps and pass your exam.
Online PCNSE free questions and answers of New Version:
NEW QUESTION 1
If the firewall is configured for credential phishing prevention using the “Domain Credential Filter” method, which login will be detected as credential theft?
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference: https://www.paloaltonetworks.com/documentation/80/pan-os/newfeaturesguide/content-inspection-features/credential-phishing-prevention
NEW QUESTION 2
The web server is configured to listen for HTTP traffic on port 8080. The clients access the web server using the IP address 1.1.1.100 on TCP Port 80. The destination NAT rule is configured to translate both IP address and report to 10.1.1.100 on TCP Port 8080.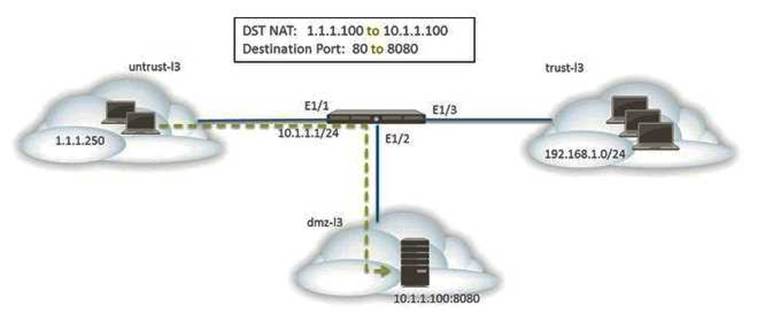
Which NAT and security rules must be configured on the firewall? (Choose two)
- A. A security policy with a source of any from untrust-I3 Zone to a destination of 10.1.1.100 in dmz-I3 zone using web-browsing application
- B. A NAT rule with a source of any from untrust-I3 zone to a destination of 10.1.1.100 in dmz-zone using service-http service.
- C. A NAT rule with a source of any from untrust-I3 zone to a destination of 1.1.1.100 in untrust-I3 zone using service-http service.
- D. A security policy with a source of any from untrust-I3 zone to a destination of 1.1.100 in dmz-I3 zone using web-browsing application.
Answer: BD
NEW QUESTION 3
Given the following table.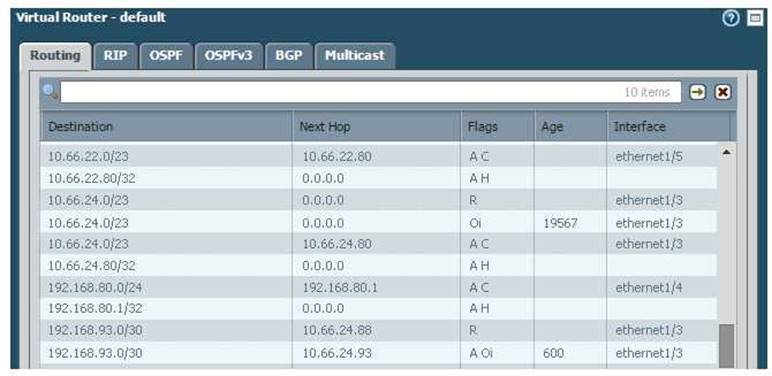
Which configuration change on the firewall would cause it to use 10.66.24.88 as the next hop for the 192.168.93.0/30 network?
- A. Configuring the administrative Distance for RIP to be lower than that of OSPF Int.
- B. Configuring the metric for RIP to be higher than that of OSPF Int.
- C. Configuring the administrative Distance for RIP to be higher than that of OSPF Ext.
- D. Configuring the metric for RIP to be lower than that OSPF Ext.
Answer: A
NEW QUESTION 4
Which three options are supported in HA Lite? (Choose three.)
- A. Virtual link
- B. Active/passive deployment
- C. Synchronization of IPsec security associations
- D. Configuration synchronization
- E. Session synchronization
Answer: BCD
Explanation:
Reference: https://www.paloaltonetworks.com/documentation/80/pan-os/web-interface-help/device/device-high-availability/ha-lite
NEW QUESTION 5
A company hosts a publically accessible web server behind a Palo Alto Networks next generation firewall with the following configuration information.
Users outside the company are in the "Untrust-L3" zone The web server physically resides in the "Trust-L3" zone. Web server public IP address: 23.54.6.10
Web server private IP address: 192.168.1.10
Which two items must be NAT policy contain to allow users in the untrust-L3 zone to access the web server? (Choose two)
- A. Untrust-L3 for both Source and Destination zone
- B. Destination IP of 192.168.1.10
- C. Untrust-L3 for Source Zone and Trust-L3 for Destination Zone
- D. Destination IP of 23.54.6.10
Answer: CD
NEW QUESTION 6
A network administrator uses Panorama to push security polices to managed firewalls at branch offices. Which policy type should be configured on Panorama if the administrators at the branch office sites to override these products?
- A. Pre Rules
- B. Post Rules
- C. Explicit Rules
- D. Implicit Rules
Answer: A
NEW QUESTION 7
Several offices are connected with VPNs using static IPv4 routes. An administrator has been tasked with implementing OSPF to replace static routing.
Which step is required to accomplish this goal?
- A. Assign an IP address on each tunnel interface at each site
- B. Enable OSPFv3 on each tunnel interface and use Area ID 0.0.0.0
- C. Assign OSPF Area ID 0.0.0.0 to all Ethernet and tunnel interfaces
- D. Create new VPN zones at each site to terminate each VPN connection
Answer: C
NEW QUESTION 8
Which three authentication factors does PAN-OS® software support for MFA (Choose three.)
- A. Push
- B. Pull
- C. Okta Adaptive
- D. Voice E.SMS
Answer: ADE
Explanation:
Reference: https://www.paloaltonetworks.com/documentation/80/pan-os/pan-os/authentication/configure-multi-factor-authentication
NEW QUESTION 9
If an administrator does not possess a website’s certificate, which SSL decryption mode will allow the Palo Alto networks NGFW to inspect when users browse to HTTP(S) websites?
- A. SSL Forward Proxy
- B. SSL Inbound Inspection
- C. TLS Bidirectional proxy
- D. SSL Outbound Inspection
Answer: A
NEW QUESTION 10
Which feature must you configure to prevent users form accidentally submitting their corporate
credentials to a phishing website?
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference: https://www.paloaltonetworks.com/documentation/80/pan-os/pan-os/threat-prevention/prevent-credential-phishing
NEW QUESTION 11
Palo Alto Networks maintains a dynamic database of malicious domains.
Which two Security Platform components use this database to prevent threats? (Choose two)
- A. Brute-force signatures
- B. BrightCloud Url Filtering
- C. PAN-DB URL Filtering
- D. DNS-based command-and-control signatures
Answer: CD
NEW QUESTION 12
How are IPV6 DNS queries configured to user interface ethernet1/3?
- A. Network > Virtual Router > DNS Interface
- B. Objects > CustomerObjects > DNS
- C. Network > Interface Mgrnt
- D. Device > Setup > Services > Service Route Configuration
Answer: D
NEW QUESTION 13
An administrator needs to determine why users on the trust zone cannot reach certain websites. The only information available is shown on the following image. Which configuration change should the administrator make?
A)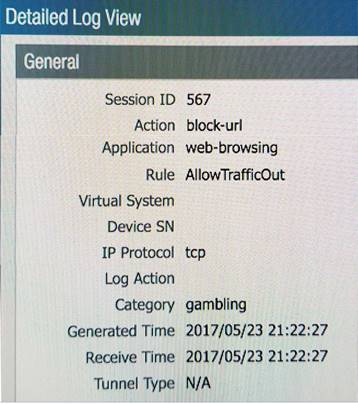
B)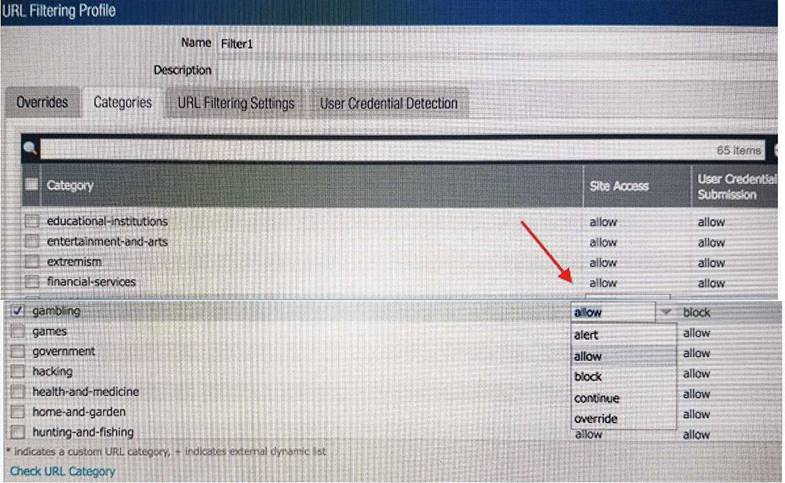
C)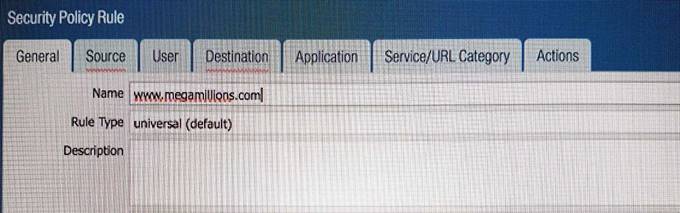
D)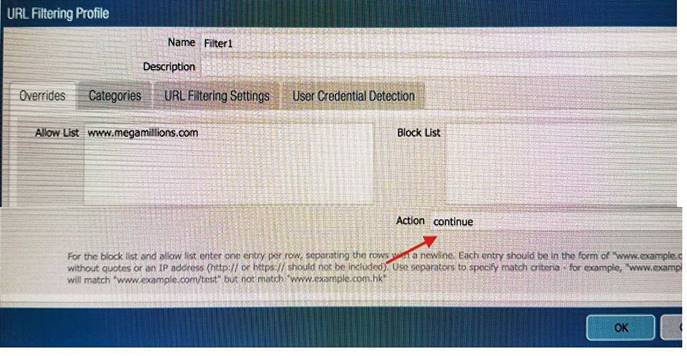
E)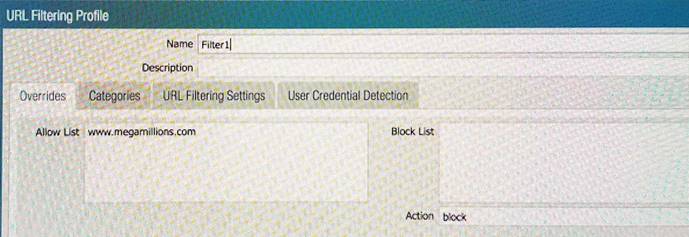
- A. Option A
- B. Option B
- C. Option C
- D. Option D
- E. Option E
Answer: B
NEW QUESTION 14
Which Security policy rule will allow an admin to block facebook chat but allow Facebook in general?
- A. Deny application facebook-chat before allowing application facebook
- B. Deny application facebook on top
- C. Allow application facebook on top
- D. Allow application facebook before denying application facebook-chat
Answer: A
Explanation:
Reference: https://live.paloaltonetworks.com/t5/Configuration-Articles/Failed-to-Block-Facebook-Chat-Consistently/ta-p/115673
NEW QUESTION 15
Which data flow describes redistribution of user mappings?
- A. User-ID agent to firewall
- B. firewall to firewall
- C. Domain Controller to User-ID agent
- D. User-ID agent to Panorama
Answer: B
NEW QUESTION 16
Which option is an IPv6 routing protocol?
- A. RIPv3
- B. OSPFv3
- C. OSPv3
- D. BGP NG
Answer: B
NEW QUESTION 17
Refer to the exhibit.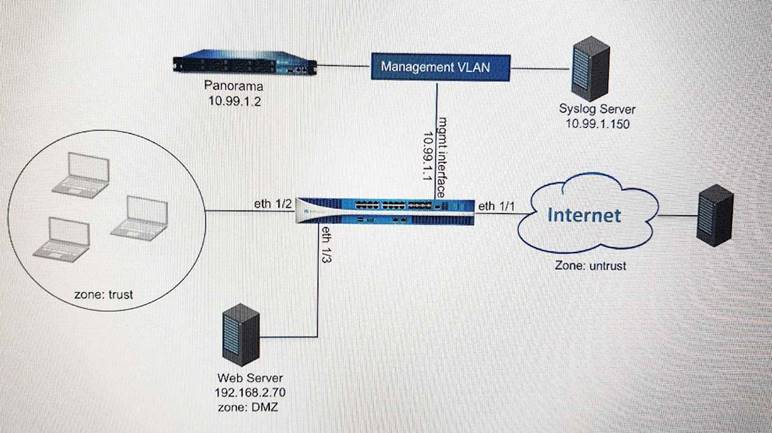
An administrator cannot see any of the Traffic logs from the Palo Alto Networks NGFW on Panorama. The configuration problem seems to be on the firewall side. Where is the best place on the Palo Alto Networks NGFW to check whether the configuration is correct?
A)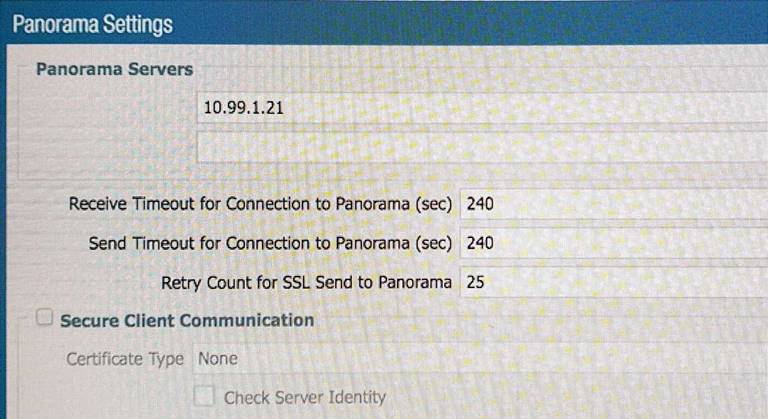
B)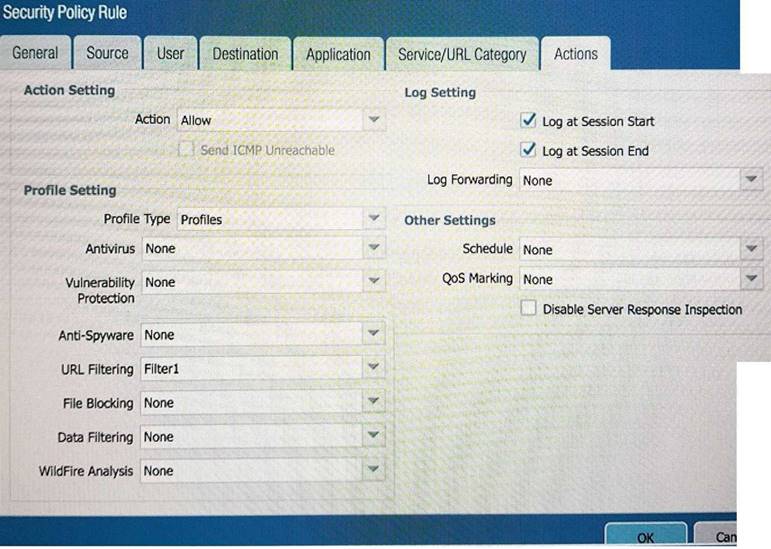
C)
D)
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 18
A client is concerned about resource exhaustion because of denial-of-service attacks against their DNS servers. Which option will protect the individual servers?
- A. Enable packet buffer protection on the Zone Protection Profile.
- B. Apply an Anti-Spyware Profile with DNS sinkholing.
- C. Use the DNS App-ID with application-default.
- D. Apply a classified DoS Protection Profile.
Answer: A
NEW QUESTION 19
Which feature prevents the submission of corporate login information into website forms?
- A. Data filtering
- B. User-ID
- C. File blocking
- D. Credential phishing prevention
Answer: D
Explanation:
Reference: https://www.paloaltonetworks.com/cyberpedia/how-the-next-generation-security-platform-contributes-to-gdpr-compliance
NEW QUESTION 20
Which two methods can be used to mitigate resource exhaustion of an application server? (Choose
two)
- A. Vulnerability Object
- B. DoS Protection Profile
- C. Data Filtering Profile
- D. Zone Protection Profile
Answer: BD
NEW QUESTION 21
An administrator has configured the Palo Alto Networks NGFW’s management interface to connect
to the internet through a dedicated path that does not traverse back through the NGFW itself.
Which configuration setting or step will allow the firewall to get automatic application signature updates?
- A. A scheduler will need to be configured for application signatures.
- B. A Security policy rule will need to be configured to allow the update requests from the firewall to the update servers.
- C. A Threat Prevention license will need to be installed.
- D. A service route will need to be configured.
Answer: D
Explanation:
The firewall uses the service route to connect to the Update Server and checks for new content release versions and, if there are updates available, displays them at the top of the list.
Reference: https://www.paloaltonetworks.com/documentation/80/pan-os/web-interface-help/device/device-dynamic-updates
NEW QUESTION 22
Which GlobalProtect Client connect method requires the distribution and use of machine certificates?
- A. User-logon (Always on)
- B. At-boot
- C. On-demand
- D. Pre-logon
Answer: D
NEW QUESTION 23
Firewall administrators cannot authenticate to a firewall GUI.
Which two logs on that firewall will contain authentication-related information useful in troubleshooting this issue? (Choose two.)
- A. ms log
- B. authd log
- C. System log
- D. Traffic log
- E. dp-monitor .log
Answer: BC
NEW QUESTION 24
VPN traffic intended for an administrator’s Palo Alto Networks NGFW is being maliciously intercepted and retransmitted by the interceptor. When creating a VPN tunnel, which protection profile can be enabled to prevent this malicious behavior?
- A. Zone Protection
- B. Replay
- C. Web Application
- D. DoS Protection
Answer: A
NEW QUESTION 25
Which CLI command enables an administrator to check the CPU utilization of the dataplane?
- A. show running resource-monitor
- B. debug data-plane dp-cpu
- C. show system resources
- D. debug running resources
Answer: A
NEW QUESTION 26
A web server is hosted in the DMZ and the server is configured to listen for incoming connections on TCP port 443. A Security policies rules allowing access from the Trust zone to the DMZ zone needs to be configured to allow web-browsing access. The web server hosts its contents over HTTP(S). Traffic from Trust to DMZ is being decrypted with a Forward Proxy rule.
Which combination of service and application, and order of Security policy rules, needs to be configured to allow cleartext web- browsing traffic to this server on tcp/443.
- A. Rule #1: application: web-browsing; service: application-default; action: allow Rule #2: application: ssl; service: application-default; action: allow
- B. Rule #1: application: web-browsing; service: service-https; action: allow Rule #2: application: ssl; service: application-default; action: allow
- C. Rule # 1: application: ssl; service: application-default; action: allowRule #2: application: web-browsing; service: application-default; action: allow
- D. Rule #1: application: web-browsing; service: service-http; action: allow Rule #2: application: ssl; service: application-default; action: allow
Answer: A
NEW QUESTION 27
A client has a sensitive application server in their data center and is particularly concerned about session flooding because of denial of-service attacks.
How can the Palo Alto Networks NGFW be configured to specifically protect this server against session floods originating from a single IP address?
- A. Define a custom App-ID to ensure that only legitimate application traffic reaches the server
- B. Add QoS Profiles to throttle incoming requests
- C. Add a tuned DoS Protection Profile
- D. Add an Anti-Spyware Profile to block attacking IP address
Answer: C
NEW QUESTION 28
An administrator has been asked to configure a Palo Alto Networks NGFW to provide protection against worms and trojans. Which Security Profile type will protect against worms and trojans?
- A. Anti-Spyware
- B. WildFire
- C. Vulnerability Protection
- D. Antivirus
Answer: A
Explanation:
Reference: https://www.paloaltonetworks.com/documentation/71/pan-os/pan-os/policy/antivirus- profiles
NEW QUESTION 29
What can missing SSL packets when performing a packet capture on dataplane interfaces?
- A. The packets are hardware offloaded to the offloaded processor on the dataplane
- B. The missing packets are offloaded to the management plane CPU
- C. The packets are not captured because they are encrypted
- D. There is a hardware problem with offloading FPGA on the management plane
Answer: A
NEW QUESTION 30
If the firewall has the link monitoring configuration, what will cause a failover?
- A. ethernet1/3 and ethernet1/6 going down
- B. ethernet1/3 going down
- C. ethernet1/3 or Ethernet1/6 going down
- D. ethernet1/6 going down
Answer: A
NEW QUESTION 31
......
P.S. DumpSolutions now are offering 100% pass ensure PCNSE dumps! All PCNSE exam questions have been updated with correct answers: https://www.dumpsolutions.com/PCNSE-dumps/ (255 New Questions)


