312-50v11 Exam Questions - Online Test
312-50v11 Premium VCE File

150 Lectures, 20 Hours
Exam Code: 312-50v11 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: Certified Ethical Hacker Exam (CEH v11)
Certification Provider: EC-Council
Free Today! Guaranteed Training- Pass 312-50v11 Exam.
Also have 312-50v11 free dumps questions for you:
NEW QUESTION 1
What hacking attack is challenge/response authentication used to prevent?
- A. Replay attacks
- B. Scanning attacks
- C. Session hijacking attacks
- D. Password cracking attacks
Answer: A
NEW QUESTION 2
In the context of password security, a simple dictionary attack involves loading a dictionary file (a text file full of dictionary words) into a cracking application such as L0phtCrack or John the Ripper, and running it against user accounts located by the application. The larger the word and word fragment selection, the more effective the dictionary attack is. The brute force method is the most inclusive, although slow. It usually tries every possible letter and number combination in its automated exploration. If you would use both brute force and dictionary methods combined together to have variation of words, what would you call such an attack?
- A. Full Blown
- B. Thorough
- C. Hybrid
- D. BruteDics
Answer: C
NEW QUESTION 3
One of your team members has asked you to analyze the following SOA record.
What is the TTL? Rutgers.edu.SOA NS1.Rutgers.edu ipad.college.edu (200302028 3600 3600 604800 2400.)
- A. 200303028
- B. 3600
- C. 604800
- D. 2400
- E. 60
- F. 4800
Answer: D
NEW QUESTION 4
An attacker attaches a rogue router in a network. He wants to redirect traffic to a LAN attached to his router as part of a man-in-the-middle attack. What measure on behalf of the legitimate admin can mitigate this attack?
- A. Make sure that legitimate network routers are configured to run routing protocols with authentication.
- B. Disable all routing protocols and only use static routes
- C. Only using OSPFv3 will mitigate this risk.
- D. Redirection of the traffic cannot happen unless the admin allows it explicitly.
Answer: A
NEW QUESTION 5
How can you determine if an LM hash you extracted contains a password that is less than 8 characters long?
- A. There is no way to tell because a hash cannot be reversed
- B. The right most portion of the hash is always the same
- C. The hash always starts with AB923D
- D. The left most portion of the hash is always the same
- E. A portion of the hash will be all 0's
Answer: B
NEW QUESTION 6
The establishment of a TCP connection involves a negotiation called three-way handshake. What type of message does the client send to the server in order to begin this negotiation?
- A. ACK
- B. SYN
- C. RST
- D. SYN-ACK
Answer: B
NEW QUESTION 7
Identify the web application attack where the attackers exploit vulnerabilities in dynamically generated web pages to inject client-side script into web pages viewed by other users.
- A. LDAP Injection attack
- B. Cross-Site Scripting (XSS)
- C. SQL injection attack
- D. Cross-Site Request Forgery (CSRF)
Answer: B
NEW QUESTION 8
One of your team members has asked you to analyze the following SOA record. What is the version? Rutgers.edu.SOA NS1.Rutgers.edu ipad.college.edu (200302028 3600 3600 604800 2400.) (Choose four.)
- A. 200303028
- B. 3600
- C. 604800
- D. 2400
- E. 60
- F. 4800
Answer: A
NEW QUESTION 9
Why should the security analyst disable/remove unnecessary ISAPI filters?
- A. To defend against social engineering attacks
- B. To defend against webserver attacks
- C. To defend against jailbreaking
- D. To defend against wireless attacks
Answer: B
NEW QUESTION 10
Some clients of TPNQM SA were redirected to a malicious site when they tried to access the TPNQM main site. Bob, a system administrator at TPNQM SA, found that they were victims of DNS Cache Poisoning. What should Bob recommend to deal with such a threat?
- A. The use of security agents in clients’ computers
- B. The use of DNSSEC
- C. The use of double-factor authentication
- D. Client awareness
Answer: B
NEW QUESTION 11
“........is an attack type for a rogue Wi-Fi access point that appears to be a legitimate one offered on the premises, but actually has been set up to eavesdrop on wireless communications. It is the wireless version of the phishing scam. An attacker fools wireless users into connecting a laptop or mobile phone to a tainted hot-spot by posing as a legitimate provider. This type of attack may be used to steal the passwords of
unsuspecting users by either snooping the communication link or by phishing, which involves setting up a fraudulent web site and luring people there.”
Fill in the blank with appropriate choice.
- A. Evil Twin Attack
- B. Sinkhole Attack
- C. Collision Attack
- D. Signal Jamming Attack
Answer: A
NEW QUESTION 12
You are trying to break into a highly classified top-secret mainframe computer with highest security system in place at Merclyn Barley Bank located in Los Angeles.
You know that conventional hacking doesn't work in this case, because organizations such as banks are generally tight and secure when it comes to protecting their systems.
In other words, you are trying to penetrate an otherwise impenetrable system. How would you proceed?
- A. Look for "zero-day" exploits at various underground hacker websites in Russia and China and buy the necessary exploits from these hackers and target the bank's network
- B. Try to hang around the local pubs or restaurants near the bank, get talking to a poorly-paid or disgruntled employee, and offer them money if they'll abuse their access privileges by providing you with sensitive information
- C. Launch DDOS attacks against Merclyn Barley Bank's routers and firewall systems using 100, 000 or more "zombies" and "bots"
- D. Try to conduct Man-in-the-Middle (MiTM) attack and divert the network traffic going to the Merclyn Barley Bank's Webserver to that of your machine using DNS Cache Poisoning techniques
Answer: B
NEW QUESTION 13
You are programming a buffer overflow exploit and you want to create a NOP sled of 200 bytes in the program exploit.c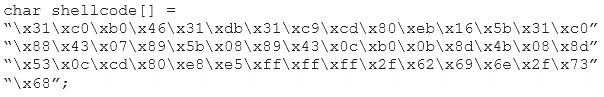
What is the hexadecimal value of NOP instruction?
- A. 0x60
- B. 0x80
- C. 0x70
- D. 0x90
Answer: D
NEW QUESTION 14
When discussing passwords, what is considered a brute force attack?
- A. You attempt every single possibility until you exhaust all possible combinations or discover the password
- B. You threaten to use the rubber hose on someone unless they reveal their password
- C. You load a dictionary of words into your cracking program
- D. You create hashes of a large number of words and compare it with the encrypted passwords
- E. You wait until the password expires
Answer: A
NEW QUESTION 15
What term describes the amount of risk that remains after the vulnerabilities are classified and the countermeasures have been deployed?
- A. Residual risk
- B. Impact risk
- C. Deferred risk
- D. Inherent risk
Answer: A
NEW QUESTION 16
Which of the following is the structure designed to verify and authenticate the identity of individuals within the enterprise taking part in a data exchange?
- A. SOA
- B. biometrics
- C. single sign on
- D. PKI
Answer: D
NEW QUESTION 17
Which Intrusion Detection System is the best applicable for large environments where critical assets on the network need extra scrutiny and is ideal for observing sensitive network segments?
- A. Honeypots
- B. Firewalls
- C. Network-based intrusion detection system (NIDS)
- D. Host-based intrusion detection system (HIDS)
Answer: C
NEW QUESTION 18
During the process of encryption and decryption, what keys are shared? During the process of encryption and decryption, what keys are shared?
- A. Private keys
- B. User passwords
- C. Public keys
- D. Public and private keys
Answer: C
NEW QUESTION 19
Fingerprinting an Operating System helps a cracker because:
- A. It defines exactly what software you have installed
- B. It opens a security-delayed window based on the port being scanned
- C. It doesn't depend on the patches that have been applied to fix existing security holes
- D. It informs the cracker of which vulnerabilities he may be able to exploit on your system
Answer: D
NEW QUESTION 20
If you want to only scan fewer ports than the default scan using Nmap tool, which option would you use?
- A. –r
- B. –F
- C. –P
- D. –sP
Answer: B
NEW QUESTION 21
......
Recommend!! Get the Full 312-50v11 dumps in VCE and PDF From Certshared, Welcome to Download: https://www.certshared.com/exam/312-50v11/ (New 254 Q&As Version)
- how many questions of 312-50v10 pdf?
- The Improved Guide To ECSAv10 Dumps Questions
- EC-Council 712-50 Dumps Questions 2021
- What Pinpoint 312-85 Actual Exam Is
- Breathing EC-Council 312-50v10 pdf
- Validated 712-50 Exam Questions 2021
- EC-Council 312-50v9 Study Guides 2021
- Download 712-50 Braindumps 2021
- Top Tips Of Abreast Of The Times 312-50v12 Practice Exam
- The Renovate Guide To 312-50v10 exam question


