156-315.80 Exam Questions - Online Test
156-315.80 Premium VCE File

150 Lectures, 20 Hours
Want to know Pass4sure 156-315.80 Exam practice test features? Want to lear more about Check-Point Check Point Certified Security Expert - R80 certification experience? Study Vivid Check-Point 156-315.80 answers to Most recent 156-315.80 questions at Pass4sure. Gat a success with an absolute guarantee to pass Check-Point 156-315.80 (Check Point Certified Security Expert - R80) test on your first attempt.
Online Check-Point 156-315.80 free dumps demo Below:
NEW QUESTION 1
Session unique identifiers are passed to the web api using which http header option?
- A. X-chkp-sid
- B. Accept-Charset
- C. Proxy-Authorization
- D. Application
Answer: C
NEW QUESTION 2
On R80.10 the IPS Blade is managed by:
- A. Threat Protection policy
- B. Anti-Bot Blade
- C. Threat Prevention policy
- D. Layers on Firewall policy
Answer: C
NEW QUESTION 3
What is the command to check the status of the SmartEvent Correlation Unit?
- A. fw ctl get int cpsead_stat
- B. cpstat cpsead
- C. fw ctl stat cpsemd
- D. cp_conf get_stat cpsemd
Answer: B
NEW QUESTION 4
What must you do first if “fwm sic_reset” could not be completed?
- A. Cpstop then find keyword “certificate” in objects_5_0.C and delete the section
- B. Reinitialize SIC on the security gateway then run “fw unloadlocal”
- C. Reset SIC from Smart Dashboard
- D. Change internal CA via cpconfig
Answer: D
NEW QUESTION 5
What two ordered layers make up the Access Control Policy Layer?
- A. URL Filtering and Network
- B. Network and Threat Prevention
- C. Application Control and URL Filtering
- D. Network and Application Control
Answer: D
NEW QUESTION 6
Fill in the blank: An identity server uses a ______ for user authentication.
- A. Shared secret
- B. Certificate
- C. One-time password
- D. Token
Answer: A
NEW QUESTION 7
Fill in the blank: The “fw monitor” tool can be best used to troubleshoot _______.
- A. AV issues
- B. VPN errors
- C. Network issues
- D. Authentication issues
Answer: C
NEW QUESTION 8
Which features are only supported with R80.10 Gateways but not R77.x?
- A. Access Control policy unifies the Firewall, Application Control & URL Filtering, Data Awareness, and Mobile Access Software Blade policies.
- B. Limits the upload and download throughput for streaming media in the company to 1 Gbps.
- C. The rule base can be built of layers, each containing a set of the security rule
- D. Layers are inspected in the order in which they are defined, allowing control over the rule base flow and which security functionalities take precedence.
- E. Time object to a rule to make the rule active only during specified times.
Answer: C
NEW QUESTION 9
What is the recommended number of physical network interfaces in a Mobile Access cluster deployment?
- A. 4 Interfaces – an interface leading to the organization, a second interface leading to the internet, a third interface for synchronization, a fourth interface leading to the Security Management Server.
- B. 3 Interfaces – an interface leading to the organization, a second interface leading to the Internet, a third interface for synchronization.
- C. 1 Interface – an interface leading to the organization and the Internet, and configure for synchronization.
- D. 2 Interfaces – a data interface leading to the organization and the Internet, a second interface for synchronization.
Answer: B
NEW QUESTION 10
Fill in the blank: A new license should be generated and installed in all of the following situations EXCEPT when _______ .
- A. The license is attached to the wrong Security Gateway.
- B. The existing license expires.
- C. The license is upgraded.
- D. The IP address of the Security Management or Security Gateway has changed.
Answer: A
NEW QUESTION 11
You want to store the GAIA configuration in a file for later reference. What command should you use?
- A. write mem <filename>
- B. show config –f <filename>
- C. save config –o <filename>
- D. save configuration <filename>
Answer: D
NEW QUESTION 12
Which of the following describes how Threat Extraction functions?
- A. Detect threats and provides a detailed report of discovered threats.
- B. Proactively detects threats.
- C. Delivers file with original content.
- D. Delivers PDF versions of original files with active content removed.
Answer: B
NEW QUESTION 13
On what port does the CPM process run?
- A. TCP 857
- B. TCP 18192
- C. TCP 900
- D. TCP 19009
Answer: D
NEW QUESTION 14
What are the blades of Threat Prevention?
- A. IPS, DLP, AntiVirus, AntiBot, Sandblast Threat Emulation/Extraction
- B. DLP, AntiVirus, QoS, AntiBot, Sandblast Threat Emulation/Extraction
- C. IPS, AntiVirus, AntiBot
- D. IPS, AntiVirus, AntiBot, Sandblast Threat Emulation/Extraction
Answer: D
NEW QUESTION 15
What scenario indicates that SecureXL is enabled?
- A. Dynamic objects are available in the Object Explorer
- B. SecureXL can be disabled in cpconfig
- C. fwaccel commands can be used in clish
- D. Only one packet in a stream is seen in a fw monitor packet capture
Answer: C
NEW QUESTION 16
If you needed the Multicast MAC address of a cluster, what command would you run?
- A. cphaprob –a if
- B. cphaconf ccp multicast
- C. cphaconf debug data
- D. cphaprob igmp
Answer: D
NEW QUESTION 17
Using mgmt_cli, what is the correct syntax to import a host object called Server_1 from the CLI?
- A. mgmt_cli add-host “Server_1” ip_address “10.15.123.10” --format txt
- B. mgmt_cli add host name “Server_1” ip-address “10.15.123.10” --format json
- C. mgmt_cli add object-host “Server_1” ip-address “10.15.123.10” --format json
- D. mgmt._cli add object “Server-1” ip-address “10.15.123.10” --format json
Answer: B
Explanation:
Example:
mgmt_cli add host name "New Host 1" ip-address "192.0.2.1" --format json
• "--format json" is optional. By default the output is presented in plain text. References:
NEW QUESTION 18
What processes does CPM control?
- A. Object-Store, Database changes, CPM Process and web-services
- B. web-services, CPMI process, DLEserver, CPM process
- C. DLEServer, Object-Store, CP Process and database changes
- D. web_services, dle_server and object_Store
Answer: D
NEW QUESTION 19
Which command is used to obtain the configuration lock in Gaia?
- A. Lock database override
- B. Unlock database override
- C. Unlock database lock
- D. Lock database user
Answer: A
Explanation:
Obtaining a Configuration Lock
NEW QUESTION 20
What is true about VRRP implementations?
- A. VRRP membership is enabled in cpconfig
- B. VRRP can be used together with ClusterXL, but with degraded performance
- C. You cannot have a standalone deployment
- D. You cannot have different VRIDs in the same physical network
Answer: C
NEW QUESTION 21
What can we infer about the recent changes made to the Rule Base?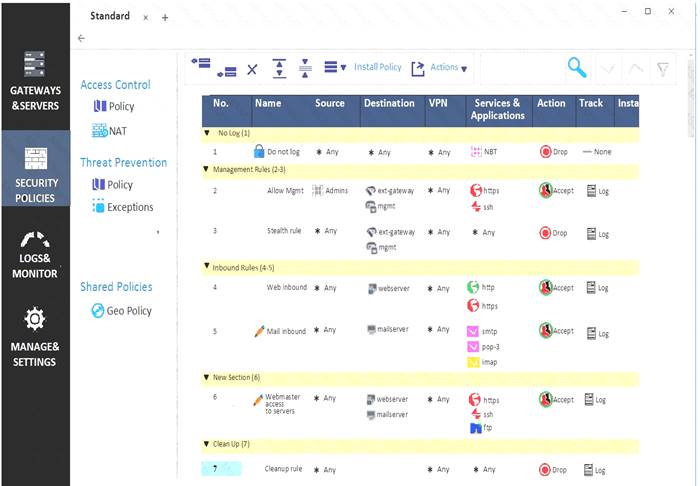
- A. Rule 7 was created by the ‘admin’ administrator in the current session
- B. 8 changes have been made by administrators since the last policy installation
- C. The rules 1, 5 and 6 cannot be edited by the ‘admin’ administrator
- D. Rule 1 and object webserver are locked by another administrator
Answer: D
NEW QUESTION 22
The Security Gateway is installed on GAIA R80. The default port for the Web User Interface is ______.
- A. TCP 18211
- B. TCP 257
- C. TCP 4433
- D. TCP 443
Answer: D
NEW QUESTION 23
Which NAT rules are prioritized first?
- A. Post-Automatic/Manual NAT rules
- B. Manual/Pre-Automatic NAT
- C. Automatic Hide NAT
- D. Automatic Static NAT
Answer: B
NEW QUESTION 24
What is the responsibility of SOLR process on R80.10 management server?
- A. Validating all data before it’s written into the database
- B. It generates indexes of data written to the database
- C. Communication between SmartConsole applications and the Security Management Server
- D. Writing all information into the database
Answer: B
NEW QUESTION 25
What CLI command compiles and installs a Security Policy on the target’s Security Gateways?
- A. fwm compile
- B. fwm load
- C. fwm fetch
- D. fwm install
Answer: B
NEW QUESTION 26
You are working with multiple Security Gateways enforcing an extensive number of rules. To simplify security administration, which action would you choose?
- A. Eliminate all possible contradictory rules such as the Stealth or Cleanup rules.
- B. Create a separate Security Policy package for each remote Security Gateway.
- C. Create network objects that restricts all applicable rules to only certain networks.
- D. Run separate SmartConsole instances to login and configure each Security Gateway directly.
Answer: B
NEW QUESTION 27
Sieve is a Cyber Security Engineer working for Global Bank with a large scale deployment of Check Point Enterprise Appliances Steve's manager. Diana asks him to provide firewall connection table details from one of the firewalls for which he is responsible. Which of these commands may impact performance briefly and should not be used during heavy traffic times of day?
- A. fw tab -t connections -s
- B. fw tab -t connections
- C. fw tab -t connections -c
- D. fw tab -t connections -f
Answer: B
NEW QUESTION 28
Can multiple administrators connect to a Security Management Server at the same time?
- A. No, only one can be connected
- B. Yes, all administrators can modify a network object at the same time
- C. Yes, every administrator has their own username, and works in a session that is independent of other administrators.
- D. Yes, but only one has the right to write.
Answer: C
NEW QUESTION 29
......
P.S. Easily pass 156-315.80 Exam with 285 Q&As Downloadfreepdf.net Dumps & pdf Version, Welcome to Download the Newest Downloadfreepdf.net 156-315.80 Dumps: https://www.downloadfreepdf.net/156-315.80-pdf-download.html (285 New Questions)
- Up To Date 156-315.80 Testing Software For Check Point Certified Security Expert - R80 Certification
- The Renovate Guide To 156-315.80 Free Practice Questions
- The Secret Of Check-Point 156-315.80 Latest Exam
- The Secret Of Check-Point 156-215.80 Free Exam Questions
- The Secret Of Check-Point 156-315.80 Exam Engine
- Regenerate 156-215.77 Keys 2021
- Top Quality Check-Point 156-315.80 Exam Online
- Leading 156-315.80 Exam Engine For Check Point Certified Security Expert - R80 Certification
- Abreast Of The Times 156-315.80 Vce For Check Point Certified Security Expert - R80 Certification


